 [Ed. GadgetTrak have replied to a number of Ryan’s criticisms — see the update at the end of this post]
[Ed. GadgetTrak have replied to a number of Ryan’s criticisms — see the update at the end of this post]
Lots of consumer electronics devices connect to a PC via a USB connection, such as mp3 players, flash drives, digital cameras and mobile phones, and the amount and range of information that they can carry is astounding — gigabytes of music, video, photos and documents. Some of these can contain important information, such as personal details or business secrets, while others may just be of sentimental value and of little interest to anyone else. In either case, losing one of these devices, be it from theft or misplacement, is at best a nuisance, and at worst can be a disaster.
GadgetTrak have developed a software system that can be installed onto supported USB devices, which they claim provides a means of tracking those devices, in the event that they are lost or stolen. Various membership options are offered, starting at $12.95 for one device, increasing to $45.95 for up to twenty devices.
There are two constituent parts to the GadgetTrak Recovery System — the software that needs to be installed onto the USB device itself and the web-based tracking service. Once your GadgetTrak account has been activated you can register your device(s) via the website, where you’re asked to enter the device type (MP3 Player, USB Flash Drive, Digital Camera, Sony PSP, GPS System, Other), manufacturer, model and serial number. Once registered, it will appear on the device list and you can edit or delete the device as expected.
Next you’re required to install the software onto your registered USB device, so that it will “phone home” once you report it as missing. To do this, you first need to download a zip archive containing the following files: a PDF with setup instructions, an autorun file, an icon file, the “phone home” application itself, and an “id” file which contains the device’s unique 40-character reference generated by the GadgetTrak website. These files (with the exception of the pdf) are then extracted to the root of the device.
How the GadgetTrak software phones home
The GadgetTrak system works in a number of ways to ensure that the protected USB device phones home automatically. Firstly, the autorun file causes the GadgetTrak application to be launched whenever the device is plugged into a computer, as well as changing the default behavior in Windows Explorer so that double clicking on the device’s icon also runs the application. Secondly, the application is named passwords.exe, and the icon is set to look like a text file. In Windows XP, with the default settings, file extensions are hidden, so to a casual viewer the device will look like it contains a text file called passwords — creating a nice little “honeytrap”. Once launched, the GadgetTrack application sends details of the device and the computer back to the GadgetTrak website.
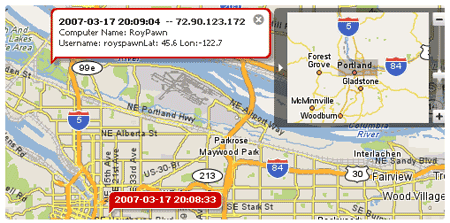
The GadgetTrak website is where you can activate the tracking system, so that you receive an email alert every time your device is been plugged into an Internet-connected computer, and finally, view a report containing the details sent back to the website when your device “phones home”. This includes the date and time of connection, the public IP address, the internal IP address, username, computer name and (approximate) location. It also displays a Yahoo! map of the location.
However, the GadgetTrak system falls down in a number of ways, by making too many assumptions in order to work:
- The USB device will be plugged into a Windows system. Only XP/2000 are supported (and Vista is partially supported according to GadgetTrak’s FAQ).
- Autorun has to be enabled. On my system, as on many others, autorun is disabled because it is an annoying feature if you are changing CDs regularly or plugging in/unplugging USB devices!
- The thief is stupid. Again, a lot of people that are more technically minded have the file extensions visible, making the idea of masquerading the executable as a text file a bit redundant, and raises the alarm straight away.
Even with these assumptions, the information that is returned when a GadgetTrak-protected device “phones home” maybe of little use. By the time you get the email report from GadgetTrak, the thief could have already passed on the device, which means that any information you’re given might point to an innocent party. Also an intelligent thief could share the “phone home” application and ID files over the web, disguised as another legitimate program, causing false reports from numerous locations.
I was also quite disappointed that the program made no attempt to encrypt the data on the device once it has been flagged as stolen or lost. It is one thing notifying the website where the device may possibly be, but if the data can be siphoned off and passed on, then the damage may already be done before it can be recovered.
Verdict
 All in all, I can see the GadgetTrak system having limited use in the real world, although it maybe more viable in a University or company campus environment, where the network can be more easily interrogated. Another point worth mentioning is the GadgetTrak Labels – which work in reverse the “phone home” approach. If the device has a GadgetTrack label on it, the finder can enter the unique code into the GadgetTrak website to arrange for anonymous communication to allow the safe return of the item.
All in all, I can see the GadgetTrak system having limited use in the real world, although it maybe more viable in a University or company campus environment, where the network can be more easily interrogated. Another point worth mentioning is the GadgetTrak Labels – which work in reverse the “phone home” approach. If the device has a GadgetTrack label on it, the finder can enter the unique code into the GadgetTrak website to arrange for anonymous communication to allow the safe return of the item.
Update: In an email sent a few hours after we published our review, GadgetTrak have attempted to address a number of our criticisms.
We actually have a Mac solution that will be available this week. Also regarding your comment about the “real world”, of the 5 devices that have been reported stolen in the past two months we have recovered 4 for our subscribers. In our experience and in discussions with law enforcement, thieves are usually in a hurry and nervous, the first thing they do when they steal an iPod or other device is remove anything that can identify the original owner, for iPods this means they will access the USB partition to look for any files that can finger the original owner, it is the same with other devices such as GPS systems and USB flash drives. Yes, you may have autorun disabled but that is quite rare actually and requires some knowledge to implement on a system, considering most opt for the default installation our solution will work the majority of the time. Think about a thief, odds are that they are not gainfully employed and as such probably lack the technical skills of folks reading this blog. To your point about the Passwords file, our recent recovery had 10 connections in a row, this meant the thief accessed the USB partition and kept on clicking the passwords file trying to open it. Technical geeks such as ourselves are much more likely to be the victims of gadget theft, than the perpetrators.

Even though it would be a little hard and probably costly to locate the device once it’s lost in the real world I still like the idea.
I think once the technology gets even smaller you’ll be able to implement a GPS chip into any device you want. A good example is cell phones, you have a lot of new smart phones that are coming out with this technology and manufacturers are providing software developers with SDK’s that will allow us to send friendly signal with our location.
I guess that would require both GPS and some type of data transmission but hey we’re in the 21st century, that technology is not there yet 🙂
Can I put that on my kid’s back pack?
This wouldn’t work at all. Whats the point of seeing a rough idea of where you device is? What if it’s in a block of apartments? You going to knock on all the doors to get it back??
Plus, today with the Internet getting ever and ever more unsafe – 99% of people have a firewall installed, even Windows firewall would alert you that something called password.exe has just tried to access the Internet. I would cancel the request and delete passwords.exe ASAP! Now whats Giga going to do?
I think if you were going to make this work, it would have to be incredibly difficult to foil… this isn’t!
And with the idea of putting GPS in a keydrive? Pointless! They are so cheap these days – if you want to have sensitive or irreplaceable data on a key drive dangling off you key ring you need your head testing! Instead buy a credit card style usb drive and pop it in your wallet. Much better!
Em22,
Have you tried the software? With the IP address and other information collected law enforcement can get more information including the exact address from the ISP, you are not paying just for the software but the service behind it. Most free firewalls are circumvented by the GadgetTrak agent, the better ones of course are not, such as those you will find in a corporate environment. The product is not meant for USB drives, but for more expensive items such as iPods, digital cameras, GPS systems and more.
It is so funny how the reviewer assumes that a theif will have such advanced technical knolwedge as to subvert the software, like they are all hackers in addition to being iPod thieves are also mad haxors. It kind of reminds me of the IT guy on Saturday night live boasting his own technical know how instead of focusing on the users. I think all security software can be worked around, even alot of the sophisticated laptopl theft software etc. I think this is a novel solution to device theft, although not perfect, it is the only solution that anyone has come up with so far. Seriously does anyone know of a better solution? I just did a search and could not find anything out there.
Ryan, if you think that enabling file extensions is advanced technical knowledge, I don’t see how you’re posting here without the help of your grandmother.
I am from Nigeria.I love your tracking technology.
What are your dealership or representative rules.
I would like to introduce your products in Nigeria
THANKS FOR YOUR COOPERATION
Yours sincerely
Oster Udech
Nos.6 gabros crescent,Otolo,P.o.box 1749,Otolo,Nnewi,Anambra state,
Nigeria.
i like the idea of GadgetTrak a lot, and in theory, it’s exactly the kind of software i was looking for when i found this page.
however, as the review states (justly), it does rely on a few key assumptions, and well, it doesn’t work on a Mac. each of those assumptions (and the Windows-only) decrease the effectiveness of the software.
i’d prefer for the software to be much more hardcore, much more stealth (such as operating in a hidden partition), and work on Macs and PCs without buying the software twice.
that said, since i am in a university setting, i’ll probably buy a GadgetTrak license — as soon as i buy a new USB drive to replace the one that i lost yesterday!
I would like to know how it has worked for someone who has a lack of police support. We recently had a HTC P4300 stolen, we have the number and first name of the person who had the sim card (stupid idiot answered some text messages we sent him – annoyed him — and returned the sim card – but said he found the card… and didn’t have the phone), and is all over our phone bill for calls made to/from that he did (so we found out a month later – since the phone company will not give you any phone numbers that are being accessed from your phone)… and the cops refuse to even talk to him about it…. and say just file the paperwork (but we won’t do anything with it….). These cops are totally useless! The cops here no blame it on the “cuts” however ones without “cuts” are doing the same crappy job! Heaven sakes… we have the person for them! If they just went to his house – they’d probably find lots of stolen goods!
We want to track the person down if they steal another one of our phones… and recover our own phone if at all possible. We can’t get a hold of the person’s address for the last phone – or we’d go recover it now… I have a hubby that doesn’t always keep his phone right next to him at all times… and the phone was left out in his truck. He isn’t eligible for insurance anymore because of the theft of his phone x2.
Ryan, if you think that enabling file extensions is advanced technical knowledge, I don't see how you're posting here without the help of your grandmother.